The piece examines 08002606490 as a telecom line with both inbound and outbound activity, focusing on patterns, routing, queuing, and pacing. It outlines ownership, typical operations, and call behaviors, presenting data points from history and verification steps. Red flags such as outbound spikes and inconsistent caller-ID are noted alongside legitimate use cases. The discussion underscores disciplined verification and evidence documentation, then signals that further analysis and precautions are warranted before conclusions can be drawn.
What 08002606490 Is and Who Owns It
The entry presents a neutral summary of ownership, registration, and purpose, without speculation.
It notes verified caller history and observed call pattern, framing them as data points.
This analytical snapshot supports informed assessment while preserving autonomy and freedom of inquiry.
How 08002606490 Typically Operates and Calls Patterns
08002606490 typically operates as a telecommunications line engaged in outbound and inbound call activity with a notable pattern of repeated attempts over short intervals.
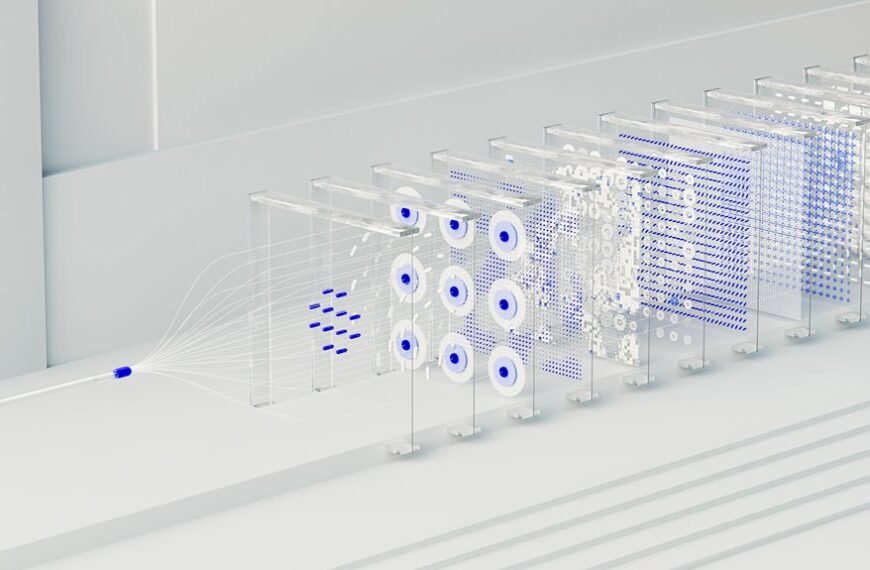
The analysis centers on how 08002606490 manages call routing, queuing, and pacing, reflecting typical operations.
It also notes phone number ownership verification steps and represents a methodical framework for assessing legitimacy and consent within this operational model.
Red Flags and Legitimate Use Cases for 08002606490
Red flags associated with 08002606490 center on deviations from standard legitimate call patterns, including abrupt spikes in outbound attempts, inconsistent caller-ID presentation, and mismatches between stated purpose and observed activity.
Analysts compare call patterns against verified norms, while delineating legitimate uses from suspicious activity.
When warranted, verification steps—though not exhaustive—support discerning intent without sensationalism or ambiguity.
How to Verify and Protect Yourself When This Number Appears
Readers proceed from the preceding assessment of red flags to a practical, methodical framework for verification and protection.
Verification tips emphasize cross-checking caller identity, corroborating purposes, and recording interactions.
Analyze caller patterns, note timing, frequency, and claimed affiliations.
Employ secure channels, avoid sharing sensitive data, and enable call screening.
Document evidence, pause before action, and escalate suspicious contacts to authorities or providers.
Maintain disciplined vigilance.
Conclusion
In summary, 08002606490 is presented as a meticulous, data-driven conduit for both inbound and outbound activity, with a rigid focus on routing, queuing, and pacing. Its patterns—repeated attempts, cross-checked identity, and corroborated purposes—suggest a disciplined, almost surgical operation. Yet red flags—sudden outbound surges and inconsistent caller IDs—signal potential anomalies. When this number appears, verification and secure channels are essential, with escalation to providers or authorities warranted if suspicious activity is detected.