A Digital Monitoring Report linked to 192.168.8.1 and its activity logs distills network behavior into a focused, evidence-driven snapshot. It maps who acted, when, and where, revealing patterns and deviations with implications for access control and policy enforcement. The report flags anomalies, uptime risks, and data handling concerns, while outlining privacy boundaries and retention needs. It presents concrete steps for governance, yet the next questions hinge on how stakeholders will translate insights into safeguards and responses.
What a Digital Monitoring Report Tells You
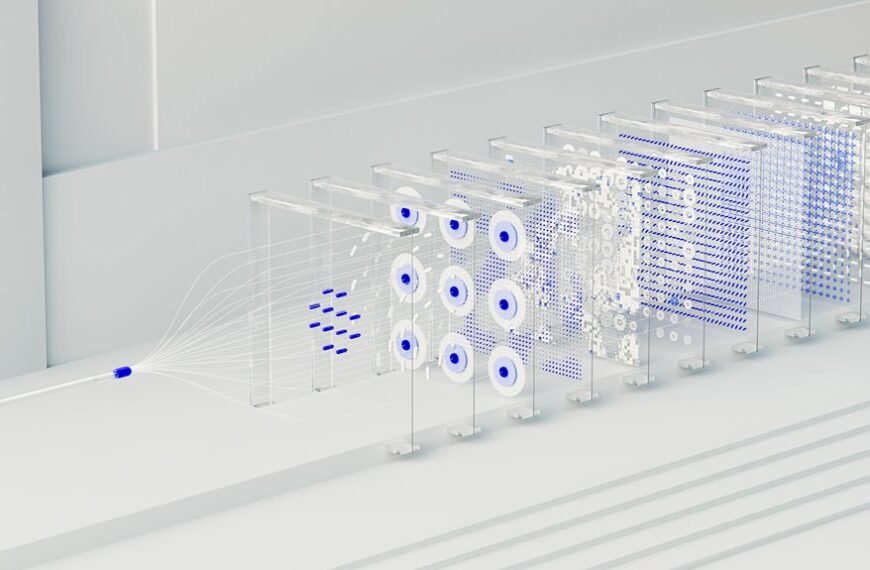
A Digital Monitoring Report distills complex data into a concise, evidence-based snapshot of system performance and behavior. It communicates trends, anomalies, and compliance implications for stakeholders who value autonomy.
The report highlights how privacy policies guide data handling and boundaries, while data retention policies define lifespan and disposal. Clarity, objectivity, and traceable metrics empower informed, responsible decision-making without overreach.
How 192.168.8.1 Logs Map Users, Times, and Destinations
The logging of 192.168.8.1 serves as a concrete example of how network activity is recorded to reveal user activity, timing, and destination endpoints.
Network tracing collects session details, enabling access control decisions and policy enforcement.
Data retention policies define retention windows.
Alert thresholds trigger notifications for unusual access, ensuring timely response while preserving privacy and operational clarity.
Interpreting Anomalies to Improve Security and Uptime
Anomalies in network activity, when properly interpreted, reveal underlying patterns that distinguish normal operations from potential threats or degraded performance.
Interpretations guide targeted responses, reducing mean time to detect and recover.
Anomaly insights feed disaster recovery planning and risk assessment, informing configuration adjustments, access controls, and monitoring thresholds to maintain uptime while preserving user freedom and system resilience.
Practical Steps to Review Permissions and Safeguard Data
Reviewing permissions and safeguarding data follows from recognizing how anomalous activity signals risk. The approach emphasizes structured privacy audits and robust access controls to minimize exposure.
Systematic reviews identify overprivileged accounts, unused permissions, and stale roles, enabling timely revocation.
Documentation and routine checks foster transparency, accountability, and user confidence, while continuous monitoring ensures deviations are promptly detected and mitigated without impeding operational freedom.
Conclusion
This Digital Monitoring Report distills network activity into a precise, evidence-based snapshot, linking 192.168.8.1 logs to user timing and destinations. It highlights trends, anomalies, and compliance implications while foregrounding privacy, retention, and disposal. By interpreting deviations with disciplined thresholds, stakeholders can strengthen access controls and uptime without impinging on legitimate user activity. Objection that monitoring erodes privacy is addressed by emphasizing purpose, scope, and data minimization, enabling transparent governance and resilient operations.