The internal address review of 10.11.12.18 compiles footprint, topology, and activity into a concise security view. It maps asset distribution, reveals address allocation patterns, and points to entry points. Reports translate observed behavior into actionable signals that expose visibility gaps and remediation priorities. The synthesis supports risk scenario planning with defined ownership and metrics, while outlining a structured path for ongoing visibility and access control improvements that invites further examination.
What 10.11.12.18 Reveals About Our Network Footprint
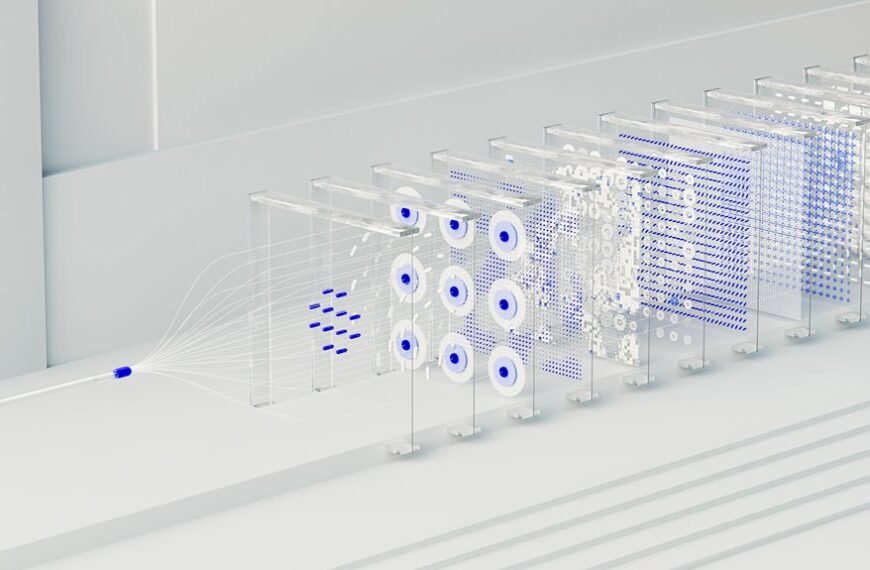
10.11.12.18 serves as a focal point for mapping the organization’s on-network assets, revealing patterns in address allocation, device distribution, and access pathways.
The analysis emphasizes 10.11.12.18 reconnaissance as a method to identify entry points and resilience factors.
Network fingerprinting procedures quantify topology, exposing clustering tendencies and circulation across segments, informing targeted, freedom-minded remediation without overreach or ambiguity.
How Reports Translate Activity Into Security Signals
How do discrete activities translate into actionable security signals? Reports aggregate behaviors into structured observations, revealing patterns and anomalies. The approach is analytical, methodical, and concise, emphasizing signal correlation across data sources. Insight gaps are identified to refine interpretations. Prioritization aligns with risk posture, while data enrichment adds context, ensuring reliable, actionable signals that support proactive defense rather than reactive responses.
Risk Scenarios From This Address and Mitigation Steps
This address presents distinct risk scenarios derived from observed activity, enabling structured assessment of potential threats and their mitigations. The analysis adopts risk mapping to identify access gaps and monitoring gaps, anchoring mitigation steps in credential exposure assessments. Anomaly detection and asset inventory data guide prioritization, while defined controls address exposure patterns, promoting resilience with concise, methodical recommendations.
Actionable Next Moves to Improve Visibility and Access Control
To enhance visibility and tighten access control, the next moves center on systematic data collection, targeted instrumentation, and disciplined policy enforcement. The analysis emphasizes identifying gaps through incremental auditing, correlating logs across systems, and establishing minimal data retention. Decisions weigh insufficient data against privacy implications, guiding scalable controls. Clear ownership, measurable metrics, and iterative reviews support disciplined, freedom-respecting governance and resilient access practices.
Conclusion
The review of 10.11.12.18 distills a precise security footprint, exposing asset distribution, address allocation patterns, and potential entry points. By mapping fingerprinting signals to access pathways, it reveals visibility gaps and prioritizes remediation with clear ownership and metrics. Risks are contextualized into actionable scenarios, guiding targeted controls without overreach. In sum, the analysis acts as a lighthouse, steadily illuminating blind spots while directing focused, iterative improvements for robust visibility and access management.