For 10.7.100.58, the analysis treats the address as a window into internal topology and exposure boundaries. Traffic patterns, access logs, and alert signals are weighed to map segment relationships and trust boundaries without assumptions. The approach emphasizes evidence, correlation, and containment readiness, while preserving artifacts for audit trails. The emerging picture invites further scrutiny of correlating events and mitigations, leaving a disciplined path forward for those who must act.
What 10.7.100.58 Reveals About Your Network Footprint
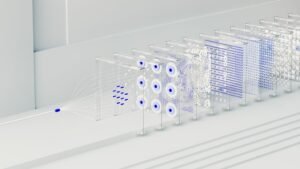
The IP address 10.7.100.58 serves as a data point indicating private network topology and internal addressing schemes, typically reflecting an enterprise or organizational segmentation rather than an external presence. This footprint interpretation highlights limited exposure and control confines, with attention to potential security incidents.
An analytical view emphasizes constrained routing, documented schematics, and risk-aware monitoring to preserve freedom and resilience.
Interpreting Traffic Patterns and Access Logs for This IP
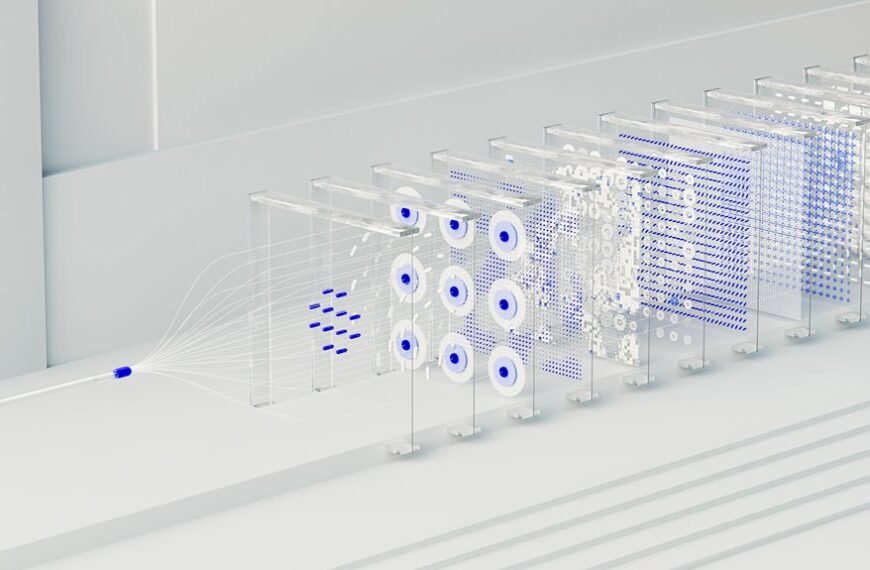
Interpreting traffic patterns and access logs for 10.7.100.58 involves a methodical examination of event timing, source and destination addresses, and protocol usage to distinguish normal operational activity from anomalies.
The analysis remains focused, yet acknowledges an unrelated topic as a tangential example, avoiding speculation.
Inference relies on concrete evidence, not off topic discussion, ensuring disciplined interpretation and traceable conclusions.
Decoding Feedback Signals: Security Alerts and Incidents
Decoding feedback signals requires a structured approach to security alerts and incidents, distinguishing actionable indicators from noise through systematic signal assessment, correlation, and verification.
The analysis treats decoding feedback as a disciplined process: data collection, anomaly detection, and event categorization align with risk priorities.
Clear, concise reporting clarifies security alerts, enabling informed decisions while preserving organizational autonomy and resilience.
Practical Steps: Investigative Workflow and Mitigation for This IP
What practical steps comprise an investigative workflow and mitigation plan for the IP 10.7.100.58, combining structured evidence gathering, targeted analysis, and containment measures to minimize risk and disruption? The workflow emphasizes network reconnaissance, credential and log verification, and rapid containment. Incident response actions isolate endpoints, preserve artifacts, and coordinate stakeholders, enabling disciplined risk reduction with clear, measurable objectives and timelines.
Conclusion
The analysis of 10.7.100.58 positions it as a controlled window into the internal topology, where traffic and logs reveal disciplined segmentation rather than random exposure. Correlated data indicate routine access patterns with constrained external reach. Feedback signals—alerts and incidents—are processed methodically, guiding rapid containment and artifact preservation. An investigative workflow ensures stakeholders stay aligned, preserving resilience. In this landscape, insights flow like a measured pulse, steady and precise, illuminating risk while sustaining operational continuity.