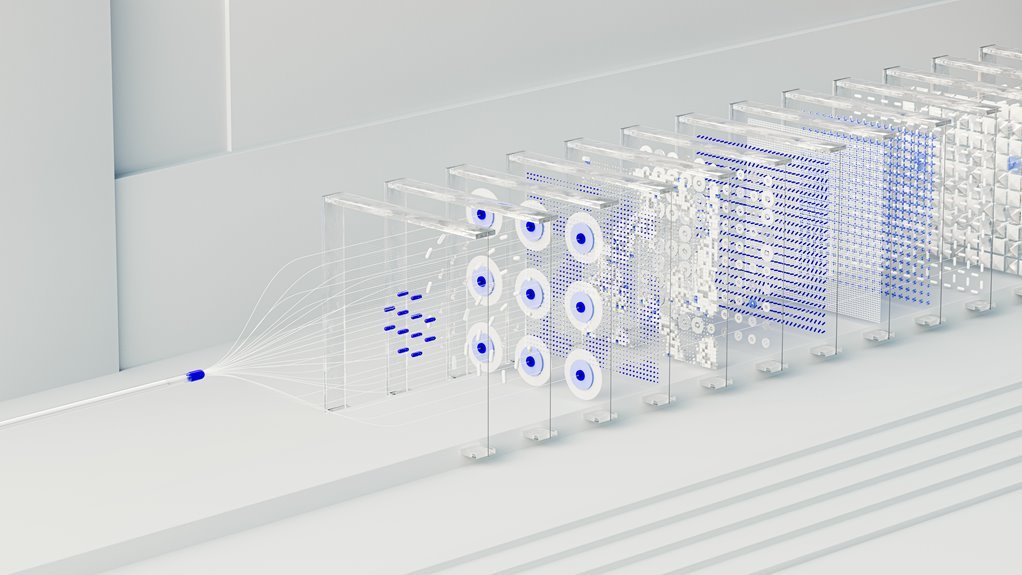
The Neural Flow 2015475477 Cyber Node represents a modular, autonomous processing construct for distributed cyber-physical systems. It emphasizes real-time learning, edge-cloud orchestration, and policy-driven workflows. The design prioritizes safety margins, data privacy, and verifiable decision-making across heterogeneous resources. Its architecture supports scalable governance and transparent computation, enabling resilient coordination under varied conditions. The implications for security, autonomy, and interoperability invite careful consideration as systems increasingly depend on such nodes, with implications that emerge beyond initial deployments.
What Is Neural Flow 2015475477 Cyber Node and Why It Matters
Neural Flow 2015475477 Cyber Node refers to a specialized computational construct designed to enable autonomous, high-fidelity data processing within a distributed cyber-physical framework. The concept centers on modular, scalable processing that supports robust decision-making. neural flow, cyber node; adaptive networks, real time learning enable Self-Contained sensing, rapid inference, and resilient coordination across heterogeneous agents, sustaining freedom through transparent, verifiable computation.
How the Cyber Node Architecture Enables Adaptive, Self-Optimizing Networks
The cyber node architecture enables adaptive, self-optimizing networks by tightly coupling modular processing with real-time learning and autonomous coordination. It supports adaptive networks through feedback-driven reconfiguration, distributed decision-making, and scalable governance.
The framework emphasizes autonomy, reliability, and portability, enabling autonomous orchestration across heterogeneous resources while preserving safety margins and clear accountability in complex, decentralized environments.
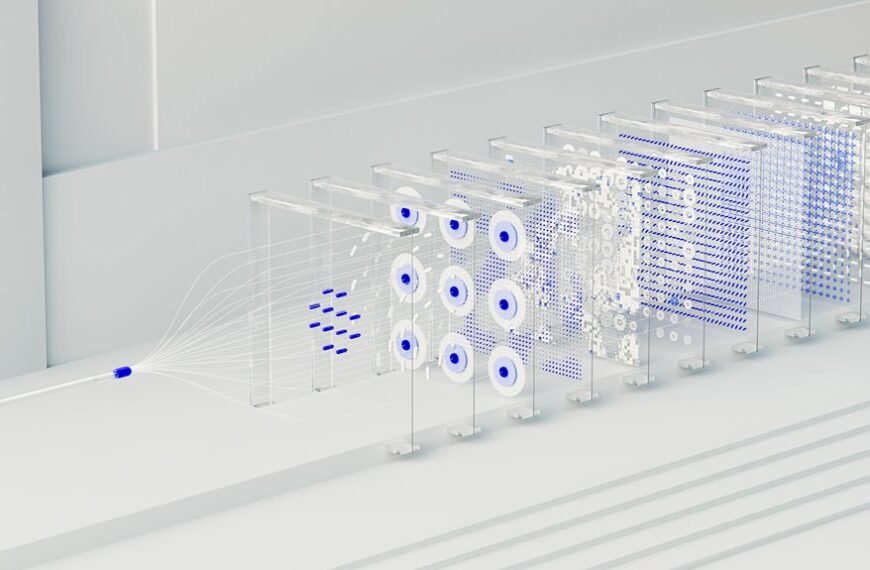
Real-Time Threat Learning and Workload Orchestration at the Edge and Cloud
The approach supports adaptive systems, autonomous management, and data privacy through edge orchestration, centralized analytics, and policy-driven adaptation, ensuring resilient performance across heterogeneous environments without compromising user freedom.
Key Components and Integration Patterns for Security, Scalability, and Autonomy
What are the essential components and integration patterns that underpin security, scalability, and autonomy in distributed cyber-physical systems? The discussion identifies adaptive security mechanisms, modular governance, and autonomous orchestration as core drivers. It emphasizes composable interfaces, event-driven workflows, and standardized protocols to enable resilient, scalable operation while preserving freedom and autonomy across heterogeneous nodes.
Conclusion
In the realm of complex systems, Neural Flow 2015475477 Cyber Node stands as a vigilant lighthouse, its beacon sweeping adaptive currents across edge and cloud. Like a seasoned conductor, it choreographs sensing, inference, and governance, never overstepping the harbor of privacy or safety. Its architecture, a disciplined map of modular components, guides autonomous ships through uncertainty, learning from waves of data and threats alike. Ultimately, it renders resilience as a calculable, verifiable habit rather than a wish.