Security Registry Notes on BX91WR and Alerts Records frame how periodic events and manual interventions align with operational cycles. The discussion emphasizes reproducible timing, interaction nuances, and governance through measurable patterns. By mapping alerts to baseline behavior and cross-validating data, signals become validated actions. The resulting playbooks support autonomous defense with accountability checkpoints, while objective metrics guide continuous improvement. The implications for workflow transparency are clear, yet critical questions remain about implementation scope and verification rigor.
What Security Registry Notes Reveal About BX91WR Activity
Initial observations of the Security Registry notes indicate a pattern of BX91WR-related entries that align with periodic system events and manual security interventions. This assessment emphasizes subtopic relevance as it connects usage motifs with operational cycles, revealing bx91wr nuances in timing and interaction.
The notes show disciplined, reproducible behavior, enabling measured interpretations of risk, control, and freedom-friendly governance.
Decoding Alerts Records: Indicators and Threat Signals
Decoding alerts records requires a systematic examination of indicators and threat signals to distinguish legitimate events from anomalies. The analysis centers on objective criteria, cross-validated data, and reproducible methods.
Alert signals are evaluated against baseline behavior, while incident trends reveal evolving tactics and frequencies. This disciplined approach supports informed decision-making, emphasizing transparency, traceability, and freedom from guesswork in security assessments.
Turning Registry Data Into Response Playbooks for BX91WR
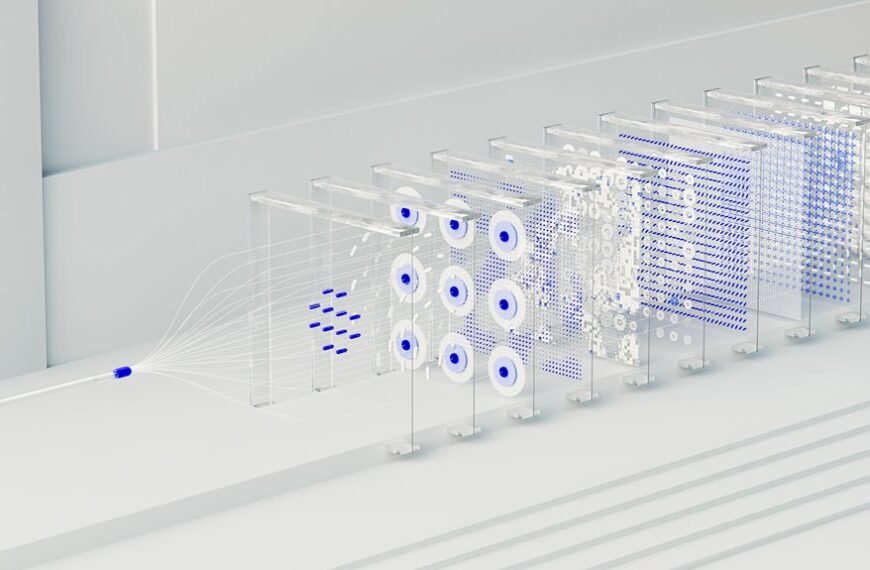
Turning registry data into actionable response playbooks for BX91WR requires a disciplined translation of raw event records into structured, repeatable frameworks.
The approach emphasizes securing telemetry and incident triage as foundational steps, converting signals into validated actions.
The analysis remains objective, concise, and methodical, outlining deterministic workflows, accountability checkpoints, and standardized playbooks that support autonomous defense while preserving operational freedom.
Practical Benchmarks: Metrics to Improve Security Posture
Practical benchmarks provide a disciplined framework for measuring security posture through objective, repeatable metrics.
The discussion analyzes how organizations use the security registry to collect data, set targets, and compare performance over time.
Metrics span detection, response, and resilience, emphasizing clarity and reproducibility.
Practical benchmarks enable informed decision-making, continuous improvement, and accountable governance without sacrificing strategic freedom.
Conclusion
This study, like a quiet oracle, alludes to a pattern beyond the numbers—BX91WR’s cadence mirrored in alerts and registry notes. The analysis yields a disciplined framework where signals translate into validated actions, and governance emerges from measurable cycles. By turning data into prescriptive playbooks, the work hints at resilience built through repeatable, accountable processes, inviting readers to map warning signs onto principled responses—as if tracing footsteps through a well-ordered corridor of security.