The Sambemil Vezkegah account owner profile centers on identity, roles, and boundary definitions, with governance and authentication framed to support auditable control. Data accessibility reflects configured permissions and session permissiveness, shaping visibility across systems for alert triage. Alerts follow a layered pipeline, ranked by risk and allocated resources accordingly. Strengthening protections and monitoring requires careful alignment of least privilege, logging, and policy enforcement, leaving questions about the remaining gaps and how they will be addressed.
What Is the Sambemil Vezkegah Account Owner Profile?
The Sambemil Vezkegah account owner profile represents the primary owner’s identity, roles, and access boundaries within the system. It documents governance responsibilities, authentication methods, and authorization scope. This profile informs privacy compliance and controls user access, ensuring appropriate privileges and audits. It enables clear accountability, mitigates risk, and supports policy-driven decisions without revealing unrelated data or operational details.
What Data Is Accessible Through the Linked Account?
What data becomes accessible through the linked account depends on the established authentication and authorization boundaries associated with the Sambemil Vezkegah profile.
Data access reflects configured permissions, scope, and session permissiveness, shaping visibility across systems.
In alert triage contexts, access confirms which alerts, logs, and metadata are available for review, correlation, and decision-making, preserving freedom to act while preserving security boundaries.
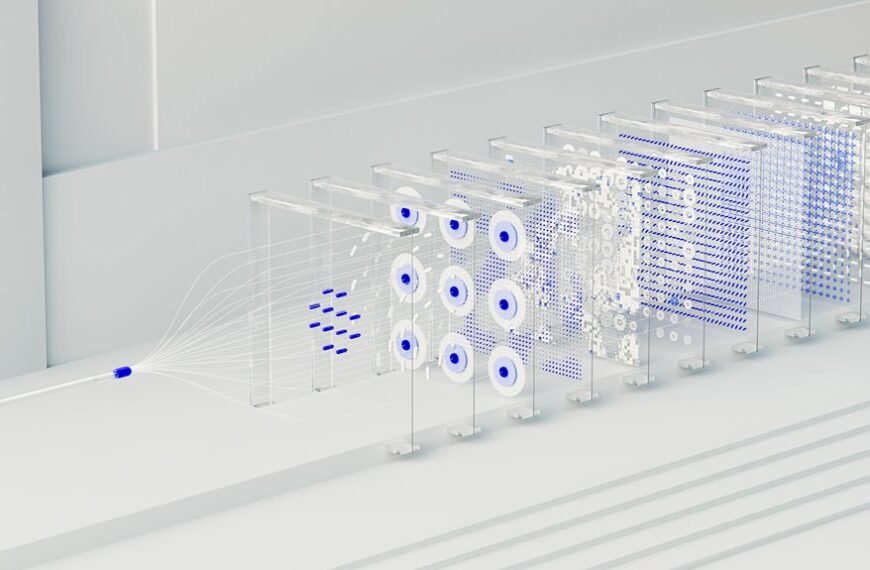
How Alerts Are Generated, Prioritized, and Triaged
Alerts are generated through a multi-layered event and telemetry pipeline that ingests signals from monitored systems, correlates related indicators, and applies predefined detection rules.
The process yields discrete alerts, which are then categorized by severity and impact.
Triage prioritization determines resource allocation, with analysts focusing on high-risk items first, followed by medium and low urgency, ensuring measurable risk reduction.
Best Practices to Strengthen Protections and Monitor Activity
The guidance emphasizes layered authentication, least privilege, and timely credential audits to reduce risk.
It highlights robust activity monitoring, anomaly detection, and rapid incident containment.
Clear governance, auditable changes, and integrated alerting sustain accountability, while empowering users with privacy-respecting mechanisms and transparent security posture assessments, including account security.
Conclusion
The Sambemil Vezkegah account owner profile centers on governance, authentication, and authorization boundaries, ensuring clear accountability. Data accessibility follows least-privilege principles, shaping system visibility and alert triage. Alerts flow through a layered pipeline, prioritized by risk and triaged to optimize resource use. An interesting statistic: organizations that implement role-based access controls reduce insider threat incidents by up to 40%. This framework therefore enhances monitoring, auditable controls, and policy-driven governance with transparent accountability.